Test out what is actually clicking on FoxBusiness.com
A overseas hacker acquired an aged copy of the U.S. government’s Terrorist Screening Database and “no fly” list from an unsecured server belonging to a industrial airline.
The Swiss hacker regarded as “maia arson crimew” blogged Thursday that she found out the Transportation Safety Administration “no fly” record from 2019 and a trove of knowledge belonging to CommuteAir on an unsecured Amazon World-wide-web Solutions cloud server utilized by the airline.
The hacker explained to The Day-to-day Dot the record appeared to have far more than 1.5 million entries. The knowledge reportedly involved names and birthdates of many people who have been barred from air journey by the govt due to suspected or recognised ties to terrorist corporations. The Daily Dot claimed that the record contains various aliases, so the range of distinctive people today on the record is far a lot less at 1.5 million.
Noteworthy people today described to be on the list contain Russian arms dealer Viktor Bout, who was a short while ago freed by the Biden administration in exchange for WNBA star Brittney Griner, and suspected associates of the IRA and many others, according to The Day-to-day Dot.
FAA REVEALS WHAT Prompted Computer OUTAGE PROMPTING Ground Halt
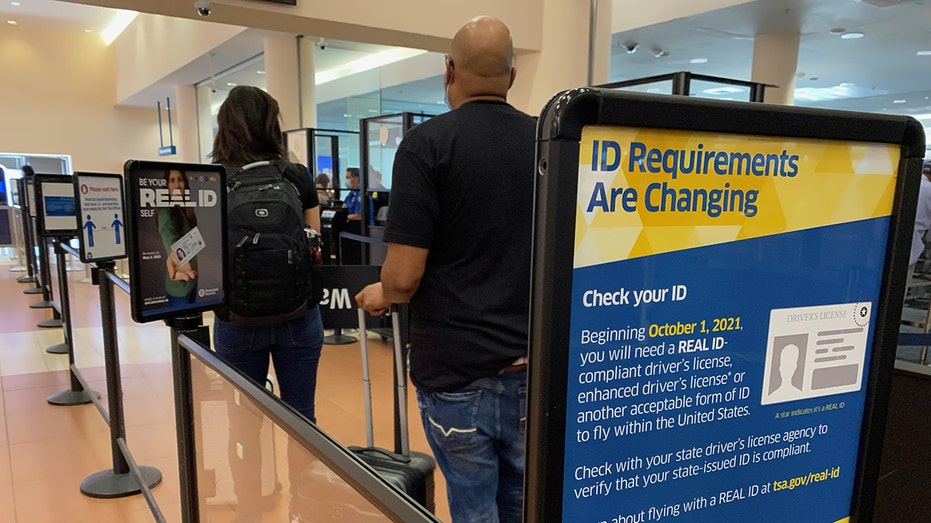
ID need signs at the entrance to the passenger TSA stability space in West Palm Seashore, Fla. (Lindsey Nicholson/UCG/Common Images Team via Getty Photographs / Getty Photos)
US EXTENDS AIR Travel COVID-19 VACCINE MANDATE FOR Intercontinental Site visitors
“It’s just mad to me how huge that terrorism screening database is, and yet there is however extremely very clear developments in the direction of virtually solely Arabic and Russian sounding names through the million entries,” crimew instructed the outlet.
Arrived at for comment, a TSA spokesman claimed the company is “conscious of a possible cybersecurity incident, and we are investigating in coordination with our federal associates.”
In a statement to FOX Small business, CommuteAir verified the legitimacy of the hacked “no fly” record and facts that contained non-public data about the firm’s workforce.

A Transportation Stability Administration pre-verify signal stands at Dulles International Airport in Dulles, Va., Aug. 19, 2015. ( Andrew Harrer/Bloomberg by using Getty Visuals / Getty Illustrations or photos)
FTX States HACKERS STOLE $415M After CRYPTOCURRENCY Exchange Filed FOR Personal bankruptcy
“CommuteAir was notified by a member of the security investigate community who recognized a misconfigured enhancement server,” reported Erik Kane, corporate communications manager for CommuteAir. “The researcher accessed data files, such as an outdated 2019 model of the federal no-fly record that involved initial and previous name and date of birth. Also, through data found on the server, the researcher uncovered entry to a databases containing particular identifiable information of CommuteAir staff members.
“Primarily based on our original investigation, no purchaser data was exposed,” Kane extra. “CommuteAir immediately took the impacted server offline and began an investigation to identify the extent of information obtain. CommuteAir has noted the details exposure to the Cybersecurity and Infrastructure Safety Agency and also notified its staff members.”

An Embraer ERJ-145XR plane operated by CommuteAir. (CommuteAir / Fox News)
CommuteAir is a regional airline started in 1989 and primarily based in Ohio. The enterprise operates with hubs in Denver, Houston and Washington Dulles and operates a lot more than 1,600 weekly flights to around 75 U.S. locations and 3 in Mexico.
Simply click Below TO Go through Additional ON FOX Small business
In accordance to crimew’s Wikipedia website page, which the hacker maintains is precise, she was indicted by a grand jury in the United States in March 2021 on criminal rates associated to her alleged hacking action concerning 2019 and 2021. Her Twitter bio describes her as “indicted hacktivist/stability researcher, artist, mentally ill enby polyam trans lesbian anarchist kitten (θΔ), 23 decades outdated.”